What Are The Roles Of A Cyber Security Professional
Roles may vary across different organizations slightly. Use the job description as a guide to what you will be expected to handle.
Sample Answer
Cyber security professionals handle access management systems. They set and manage passwords for staff members. They do regular audits to check for any irregular activity. They also choose applications that need updates and ensure they are run. They also educate the employees on how to prevent and identify malicious attacks. They work with other departments to ensure business continuity. These are tasks I have handled in my work and I would therefore make a great addition to your team.
What Are Your Greatest Strengths And Accomplishments
Take the opportunity to show how you helped your old company. Did you design its latest firewalls that prevented breaches? Did you reroute the routers? Help with information access security? Do you work well with people and show leadership skills? Talk about the types of technology you know well and how you made a positive impact in your last position. Explain how you built solid relationships with your coworkers and how you all worked together on successful projectsand how you intend to do the same at this new company.
Black Hat Hackers Vs White Hat Hackers Vs Grey Hat Hackers: Are All Illegal
Black hat hackers use cybersecurity knowledge to gain unauthorized access to networks and systems for malicious or exploitative ends. This type of hacking is illegal. Conversely, white hat hackersalso known as ethical hackersare hired to evaluate the vulnerabilities of a clients system. Because white hat hackers operate with the permission of their targets, this activity is legal. Grey hat hackers may search for system vulnerabilities without permission, but instead of exploiting the vulnerability directly may offer to fix the issue for a price. Because the intrusion was not permitted, grey hat hacking is often considered unethical and illegal.
Recommended Reading: What Are Good Job Interview Questions
How Do You Ensure That A Server Is Secure
To secure a server, it is vital to first establish a protected connection using SSH Protocol, as SSH access encrypts data transmissions. SSH uses port 22 by default, which is common knowledge to hackersso use port numbers between 1024 and 32,767 to reduce the risk of attack. You should also authenticate an SSH server using SSH keys instead of a traditional password. To secure web administration areas, deploy a Secure Socket Layer to safeguard server-client and server-server communications via the internet. Intrusion prevention software, firewalls, password requirements, and user management tactics can help maintain server security.
Top Cybersecurity Project Manager Interview Questions
So what questions can you expect in a cybersecurity project manager job interview?
Here’s a list of common questions:
38. Q: What is a data leak? How can you detect it and prevent it?
A:A data leak is when a company’s or organization’s private data is released to the public in an unauthorized manner. Data leaks can come in many ways such as hacked emails and networks, stolen or lost laptops, or released photos.
To prevent a data leak, a company needs to restrict internet uploads, add restrictions to email servers, and restrict the printing of confidential information and data.
To detect a data leak, you’ll need to:
1) Monitor access to all your networks
2) Evaluate the risk of third-parties
3) Identify and secure sensitive data
4) Encrypt data
6) Evaluate permissions across the organization
7) Use cybersecurity risk assessments
39. Q: What is a cybersecurity risk assessment?
A:A cybersecurity risk assessment is part of an organization’s risk management strategy because it helps them see how their security is performing along with current vulnerabilities and potential risks.
A cybersecurity risk assessment also covers the different types of assets owned by a company that may be prone to cyberattacks. These assets can include physical assets such as hardware, laptops, or non-physical assets such as customer data.
Companies that use a cyber risk assessment can prioritize addressing those risks based on their importance and the available budget.
– Verify the site’s security
Also Check: How To Prepare For A Telephone Interview
What Are Cyberattacks Name The Most Common Ones
Cyberattacks are malicious offensive attempts to obtain unauthorized access to a system or network in order to steal, corrupt, or destroy informationtypically for the attackers benefit.
Common types of cyberattacks include malware, phishing, man-in-the-middle attacks, SQL injections, DNS tunnelling, and zero-day exploits.
Get To Know Other Cybersecurity Students
Dylan Wood
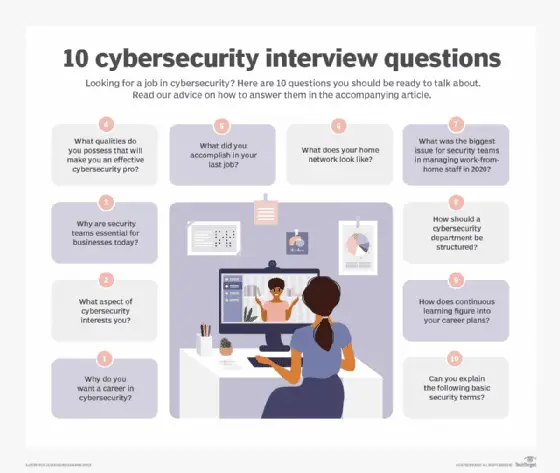
+ Cybersecurity Interview Questions And Answers To Help You Ace Your Next Interview
The job market has come a long way in the past two years with some segments witnessing higher demand than others.
Cybersecurity remains a niche industry. However, with the increase in online payments and transactions along with the rising number of fintech startups, cybersecurity analysts and project managers are in great need.
Not to mention the increasing number of cyberattacks around the world has ensured that network security and cybersecurity personnel remain in high demand everywhere.
In 2020, the global cybersecurity market was estimated to be worth $171 billion.
The cybersecurity market’s revenues are forecast to reach $146.32 billion in 2022. Meanwhile, global cybersecurity revenues are expected to continue growing by a 9.67% compound annual growth rate to $211.67 billion by 2026.
But what if you want to join the cybersecurity field, what can you expect in a cybersecurity job interview? How do businesses hire cybersecurity analysts? What types of questions do managers ask in those interviews?
And how can you, as a candidate, impress your future manager in this niche and demanding market?
Keep reading to discover the answers to these questions and more. We’ll be featuring basic and technical cybersecurity interview questions.
Read Also: Software Testing Technical Interview Questions
What Is A Cybersecurity Risk Assessment
A cybersecurity risk assessment refers to detecting the information assets that are prone to cyber-attacks and also evaluates various risks that could affect those assets.
It is mostly performed to identify, evaluate, and prioritize risks across organizations.
The best way to perform cybersecurity risk assessment is to detect:
- Relevant threats in your organization
- Internal and external vulnerabilities
- Evaluate vulnerabilities impact if they are exploited
What Is The Use Of A Firewall And How It Can Be Implemented
A firewall is a security system used to control and monitor network traffic. It is used for protecting the system/network from malware, viruses, worms, etc., and secures unauthorized access from a private network.
The steps required to set up and configure the firewall are listed below:
- Change the default password for a firewall device.
- Disable the remote administration feature.
- Configure port forwarding for specific applications to function correctly, such as an FTP server or a web server.
- Firewall installation on a network with an existing DHCP server can cause errors unless its firewalls DHCP is disabled.
- Make sure the firewall is configured to robust security policies.
Read Also: How To Study For Software Engineering Interview
How Do You Envision Your First 90 Days On The Job
Your answer should encompass how you intend to meet with your team members to find out more about them and how you can work together. You should talk about how you will prioritize gaining an understanding of what your managers need from you and what all the stakeholders hope to achieve while also building a strong rapport with your co-workers. You should ask what you can do to make an impact right away. Talk about how you intend to learn and get into the midst of business as soon as you can.
What Are Salted Hashes
When two users have the same password, it will result in the creation of the same password hashes. In such a case, an attacker can easily crack the password by performing a dictionary or brute-force attack. To avoid this, a salted hash is implemented.
A salted hash is used to randomize hashes by prepending or appending a random string to the password before hashing. This results in the creation of two completely different hashes, which can be employed to protect the users passwords in the database against the attacker.
Read Also: Where Can I Watch The Meghan Markle Interview
What Is The Cia Triad
CIA Triad is a security model to ensure IT security. CIA stands for confidentiality, integrity, and availability.
- Confidentiality: To protect sensitive information from unauthorized access.
- Integrity: To protect data from deletion or modification by an unintended person.
- Availability: To confirm the availability of the data whenever needed.
You Will Receive An Email Claiming The Sender Is From The Helpdesk Which Insists You Share Your Credentials In Order To Retrieve Your Account The Presentation Of The Contents In The Email Seems Legitimate As A User What Will You Do
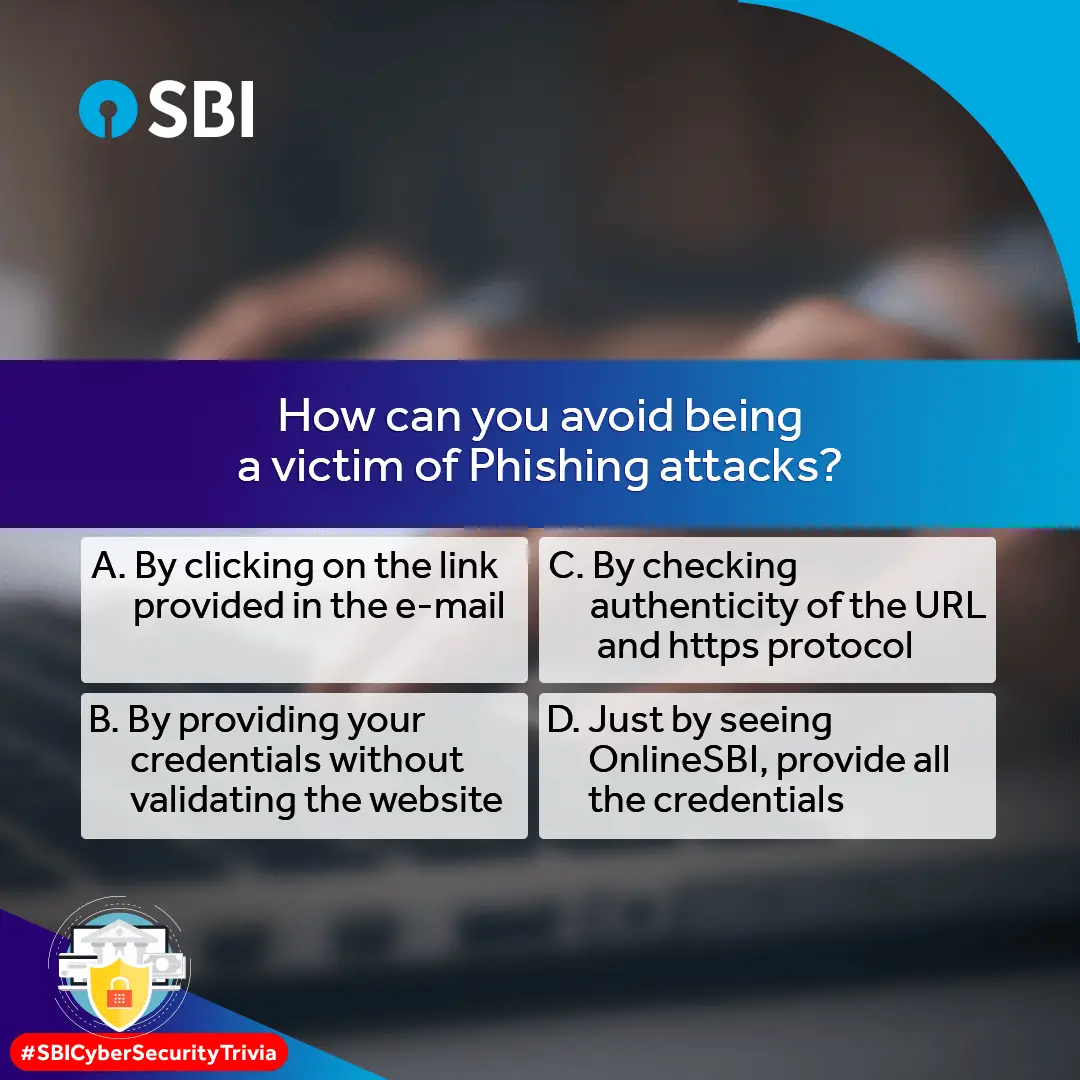
This is a classic example of a phishing email where the attacker aims to steal money by coaxing you to reveal your personal details or credentials. While these emails can often appear legitimate,one should not fall prey to them. Make sure you do not respond to such emails or even calls. It should be common knowledge that legitimate organizations never ask for personal details over calls or emails.
Read Also: How To Conduct A Phone Interview Script
Who This Course Is For:
- Fresh Graduates looking to start Cybersecurity Careers
- IT professionals wanting to move to Cybersecurity Careers
- It is from Beginners to Mid-Senior level
We are Cyber Community Formely known as cyberseclive is the team of Cyber Security Researcher and our Instructor having the Master Degree in the specialization of Cyber Security . Trained 5000+ students by my ethical hacking and bug bounty trainings. My interesting field in cybersecurity is Bug bounty, Ethical Hacking, and Security Operation Center.
4 International Research papers published in high level publications such as Elsevier and Springer. 1 Research paper in Whatsapp Forensics, 2 are in Cloud Security and 1 in Cryptography
What Do You Mean By Two
Two-factor authentication , often known as two-step verification or dual-factor authentication, is a security method in which users validate their identity using two independent authentication factors. This procedure is carried out in order to better protect the user’s credentials as well as the resources that the user has access to. Single-factor authentication , in which the user gives only one factor generally a password or passcode provides a lower level of security than two-factor authentication . Since possessing the defendant’s password alone is not enough to accomplish the authentication check, two-factor authentication adds an extra layer of security to the authentication process, making it more difficult for attackers to get access to a person’s devices or online accounts.
Also Check: What The Most Questions Asked In An Interview
What Is Data Encryption And Why It Is Important In Network Security
Data encryption is a technique used to secure the data by converting it into code. So, only authorized users can access this code or converted form of data. It is important for network security because your data can be breached at any stage in the network if it is not encrypted. In the cyber security interview questions and answers, your most questions should be on the encryption and decryption techniques and secure the network.
Did You Ever Identify An Incoming Cyber
This can give you an insight into how good the candidate is at identifying incoming attacks, be it internal or external threats. Also, it gives you a picture of how they are handled from which you can ascertain their effectiveness and the candidates ability to think/act quickly.
What Should You Look Out For?
Intricate information about the cyberattacks and the candidates responses to the same.
Also Check: How To Use Hackerrank For Interview
What Is The Difference Between Black Hat White Hat And Grey Hat Hackers
- A black-hat hacker is a person who tries to obtain unauthorized access into a system or a network to steal information for malicious purposes.
- White-hat hackers are also known as ethical hackers they are well-versed with ethical hacking tools, methodologies, and tactics for securing organization data. They try to detect and fix vulnerabilities and security holes in the systems. Many top companies recruit white hat hackers.
- A grey hat hacker is a computer security expert who may violate ethical standards or rules sometimes but does not have the malicious intent of a black hat hacker.
What Kind Of Strategies And Mindset Is Required For This Role
The interviewer is interested in whether you know the mindset and strategies that you need for this role. Share this while explaining how they will help make work easy.
Sample Answer
A cyber security professional needs to be a strategic thinker. You need to think like an attacker to identify vulnerabilities of the system. You will also need to have a long-term view in terms of how system security should be structured. Keep staff informed that their wrong use of the system may give access to attackers. They should adhere to the company security protocols. You will also need to know the attacks may come from inside the organization and therefore have a plan on what will happen if it happens.
Read Also: How To Have A Great Phone Interview
Describe Briefly About Your Experience
Sample Answer
I have five years of experience in Cyber Security I saw this as a key requirement for this position. Over the years I have handled both hardware and software systems and therefore will be great at this role. I have transferrable skills that will come in handy in his role. I have also developed soft skills such as communication and interpersonal that will contribute to the excellence of my work.
What Are The Steps To Set Up A Firewall
There are several steps followed to set up a firewall. They are:
Recommended Reading: How To Prepare For A Job Phone Interview
Have A List Of Skills To Check During The Interview
You may have a list of skills that the role requires and have included them in the job description. Make sure you have that list of skills with you during the interview.
You can compare your requirements and your candidates responses and ensure that you select candidates whose cybersecurity knowledge and skills best align with your needs.
Cyber Security Interview Questions & Answers
Cyber Security is one the popular technology in its respective field. Cyber Security will have a lot of scope in the future and Cyber Security is updating their features in the future versions. So Please be updated with the technology you are learning. We are listing out the most frequently asked and commonly asked Cyber Security questions. Just check them out.
Read Also: How To Interview For An Hr Position
What Is A Remote Desktop Protocol
Remote Desktop Protocol is developed by Microsoft, which provides GUI to connect two devices over a network.
The user uses RDP client software to serve this purpose while other device must run RDP server software. This protocol is specifically designed for remote management and to access virtual PCs, applications, and terminal server.
Describe Your Daily Routine As A Cyber Security Professional
Sample Answer
Every single day is unique depending on the issues that arise. No two days will be alike. I like to start my workday early at around 7:10 AM, the extra minutes help me prepare for the day. I follow up on security incidents that arise in the day. I ensure to identify the source and fix it. I respond to client queries and sort out access issues that are raised. I schedule short meetings in the afternoon. My workday ends at around 6 PM.
You May Like: What To Know About Sql For An Interview
Q: How Can You Prevent An Xss Attack
A:If the organization uses anti-XSS tools, I’d use those tools to create high-level encryption and prevent XSS attacks.
If the company doesn’t have anti-XSS tools, I’d create and enforce measures that guarantee user input validation and set up a CSP for the firm’s network. After that, I’d encode special characters.
What Do You Mean By Port Scanning
Ports are vital assets that are vulnerable to security breaches. Attackers use port scanning to locate open ports that are sending or receiving data on a network. This technique is also used to assess a hosts vulnerabilities by sending packets to various ports and analyzing their responses. Nevertheless, port scanning is not an inherently malicious activitycybersecurity specialists use port scanning to evaluate network security.
Read Also: How To Respond To Behavioral Interview Questions
What Are Http Response Codes
HTTP response codes display whether a particular HTTP request has been completed.
- 1xx – The request has been received, and the process is continuing.
- 2xx – The request was successfully received and accepted.
- 3xx – Further action must be taken to complete it.
- 4xx – Request cannot be fulfilled or has incorrect syntax.
- 5xx – The server fails to fulfill the request.
Advanced Cybersecurity Interview Questions
To give you an idea of the range of cyber security interview questions you may be asked, here are a few questions from top tech companies .
- What risks come with public Wi-Fi?
- What is the main difference between RSA and Diffie-Hellman?
- What is port scanning?
- What protocols fall under TCP/IP internet layer?
- Please define forward secrecy.
- Please explain the difference between stream cipher and block cipher.
- What is cognitive cyber security?
- Define a buffer overflow attack.
- What is CryptoAPI?
- What is an SQL Injection?
- What are some common types of non-physical attacks?
- What is a botnet?
- What is the difference between vulnerability assessment and penetration testing?
- Please define system hardening.
- What are the several indicators of compromise that organizations should monitor?
Previous
get started
Don’t Miss: How To Pass A Job Interview