What Does A Cybersecurity Analyst Do
Cybersecurity analysts strive to preserve the integrity of sensitive data by defending infrastructure and systems from cyberattacks. To protect these assets, cybersecurity analysts evaluate system vulnerabilities through diagnostic testing and traffic monitoring. Based on the results of these assessments, cybersecurity analysts design and implement risk management strategies. Cybersecurity analysts also respond to cyber attacks, conduct forensic analysis of previous cyber incidents, and work to ensure organizational compliance with relevant security standards and protocols.
Explain Social Engineering And Its Attacks
Social engineering is the term used to convince people to reveal confidential information.
There are mainly three types of social engineering attacks: 1) Human-based, 2) Mobile-based, and 3) Computer-based.
- Human-based attack: They may pretend like a genuine user who requests higher authority to reveal private and confidential information of the organization.
- Computer-based attack: In this attack, attackers send fake emails to harm the computer. They ask people to forward such email.
- Mobile-based attack: Attacker may send SMS to others and collect important information. If any user downloads a malicious app, then it can be misused to access authentication information.
Explain What Is Owasp Webgoat And Webscarab
- WebGoat: Its an educational tool for learning related to application security, a baseline to test security tools against known issues. Its a J2EE web application organized in Security Lessons based on tomcat and JDK 1.5.
- WebScarab: Its a framework for analysing HTTP/HTTPS traffic. It does various functions like fragment analysis, observer the traffic between the server and browser, manual intercept, session ID analysis, identifying new URLs within each page viewed
Recommended Reading: How To Ace My Interview
Q: Define The Salting Process And What Its Used For
A: Salting is the process wherein you add special characters to a password in order to make it stronger. This increases password strength in two ways: it makes it longer and it adds another set of characters that a hacker would have to guess from. Its a good measure to take for users who tend to habitually make weak passwords, but overall its a low-level defense since many experienced hackers are already familiar with the process and take it into account.
Cybersecurity Expert Master’s Program
Explain A Brute Force Attack Along With The Steps To Prevent It
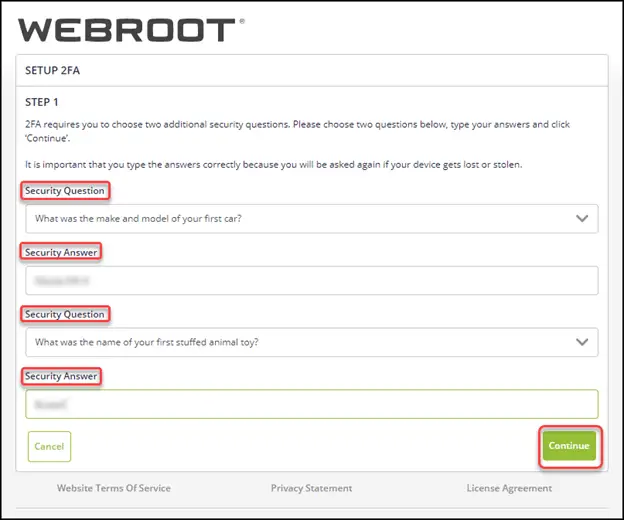
Brute force attacks strive to unlock password-protected assets by repetitively entering authentication credentials either manually or via automated credential stuffing . To prevent brute force attacks, cyber security professionals should:
- Make unique login URLs for various user groups.
- Monitor server logs and analyzes log files.
- Use two-Factor Authentication.
- Limit logins to a particular IP address or range.
- Implement CAPTCHA as part of the login process to prevent automated attacks.
- Throttle login attempts .
- Make the root user inaccessible via SSH.
Read Also: What Type Of Questions Should You Ask In An Interview
Q1: Mention What Flaw Arises From Session Tokens Having Poor Randomness Across A Range Of Values
Answer:
Session hijacking, is the issue related to A2: 2017 Broken Authentication. It is also called cookie hijacking. In this type of attack, there is the possibility of exploitation of a valid computer sessionsometimes also called a session keyto gain unauthorized access to information or services in a system. This flaw comes when there is a poor randomness in session key.
In Our Computing Labs Print Billing Is Often Tied To The Users Login Sometimes People Call To Complain About Bills For Printing They Never Did Only To Find Out That The Bills Are Indeed Correct
What do you infer from this situation? Justify.
Sometimes they realize they loaned their account to a friend who couldnt remember his/her password, and the friend did the printing. Thus the charges. Its also possible that somebody came in behind them and used their account
This is an issue with shared or public computers in general. If you dont log out of the computer properly when you leave, someone else can come in behind you and retrieve what you were doing, use your accounts, etc. Always log out of all accounts, quit programs, and close browser windows before you walk away.
Don’t Miss: What Are Good Things To Say In An Interview
What Is Host Intrusion Detection System
The Host-based intrusion detection systems are applications that operate on information collected from individual computer systems and serves on the existing system and compare with the previous mirror/snapshot of the system and validates for whether any data modification or manipulation has been done and generates an alert based on the output.
It can also figure out which processes and users are involved in malicious activities.
How Can One Set Up Application Security
First, we have to implement a secure SDLC framework for our project, i.e., software development. Then, I should know about the open web application security project and enhance my skills in the updated threats. Then, notice the security requirements for the application from the beginning stage of the development and maintenance industry application security practices as much as quickly.
After that, one should implement secure application design and architecture. The next step is implementing best and safe coding practices, including input validation, authorization, and authentication. Finally, ensure well-rounded security of the application for the coding cycle to implant a culture of secure coding cryptography, session management, and error handling at the stage of the secure SDLC.
And still think that the vulnerabilities exist, rate them and publish comprehensive reports about associated risks and alleviations of the exposures. After everything completes, its essential to scan the entire application using tools like AppScan, Fortify, etc., to conduct various tests such as Static Application Security Testing, Dynamic Application Security Testing, Angle sign-on, and Encryption. Then the software code review process will be undertaken and ensures that the most emitted phase, Post-deployment, and maintenance is secure at all levels.
So, implementing Application security for web applications is essential as the functionality and design of the applications.
Recommended Reading: How To Train Managers To Interview
Can I Attend A Demo Session Before Enrollment In This Cyber Security Course
We have a limited number of participants in a live session to maintain the Quality Standards. So, unfortunately participation in a live class without enrolment is not possible. However, you can go through the sample class recording and it would give you a clear insight about how the cyber security classes are conducted, quality of instructors and the level of interaction in the class.
What Is Shoulder Surfing
Should surfing is a method of data theft by which a bad actor peers over the shoulder of a target in order to steal confidential information like passwords and PIN numbers that can later be used to initiate a cyberattack. Like phishing, shoulder surfing is a social engineering techniquemeaning it belongs to a class of information security attacks that rely on psychological manipulation to extract confidential information or influence victims to perform actions counter to their best interests.
Don’t Miss: How To Crack A Google Interview
What Is The Most Challenging Project You Encountered On Your Learning Journey
Everyone makes mistakes, and no one is good at everything. Dig into your past: You might have overseen the response to a breach or some other serious problem. It might not have been your fault, but how you handled it shows your professionalism and problem-solving abilities. Demonstrate that you are willing and able to learn from mistakes. Explain how you took responsibility and stepped up to be a leader, and discuss how youll apply what you learned in your new role.
State The Difference Between Private And Public
In the case of digital signing, the sender uses the private key to sign the data and on the other hand receiver verifies and validates the data with the public key of the sender itself.
While in encryption, the sender encrypts the data with the public key of the receiver and receiver decrypt and validates it using his/her private key.
You May Like: What Should You Say In A Job Interview
Below Is A List Of Passwords Pulled Out A Database
A. @#$)*& ^%
Which of the following passwords meets UCSCs password requirements?
Answer is UcSc4Evr!
This is the only choice that meets all of the following UCSC requirements:
At least 8 characters in length
Contains at least 3 of the following 4 types of characters: lower case letters, upper case letters, numbers, special characters
Not a word preceded or followed by a digit
Describe Owasp Also Tell Us About The Owasp Top 10 2021
The nonprofit group OWASP publishes a list of the most prevalent web vulnerabilities. It functions as a network of cybersecurity experts who are continually working to create an ecosystem for spreading knowledge about secure online apps. Recent updates to OWASP’s top 10 vulnerabilities for 2021 include:
- A01:2021-Broken Access Control
- A08:2021-Software and Data Integrity Failures
- A09:2021-Security Logging and Monitoring Failures
- A10:2021-Server-Side Request Forgery
Read Also: How To Conduct A Job Interview Questions To Ask
What Exactly Do You Mean By Security Testing
One of the most important kinds of software testing is security testing. Before an app is made available to the public, it must be completed. This kind of testing finds weaknesses in software, including network- or web-based applications. As a result, it defends against assaults and intrusions. Any sensitive data in an app is secured from leaking thanks to security testing. It is also important to note that an organization or developer must perform it frequently to find and address various vulnerabilities, similar to any other form of software testing.
Application Security Engineer Interview Questions
Read Also: How To Send Email To Follow Up After Interview
Java Security Interview Questions
Security related consideration can be split into these parts
- User Authentication and Authorization
Following are the important considerations:
- Proper separation of authenticated and unauthenticatedresources. These can be split into separate deployable units ifpossible.
- Proper use of filters to ensure that the configuration forauthenticated resources is centralized.
- Use a proper framework like Spring Security to implementauthorization.
OWASP is normally agreat starting point. Important factors to consider are
- Validaton of user data : Ensure they are validated also inBusiness Layer.
- SQL Injection : Never build sql queries using stringconcatenation. Use a Prepared Statement. Even better, use SpringJDBCTemplate or frameworks like Hibernate, iBatis to handlecommunication with database.
- XSS – Cross Site Scripting : Ensure you check against a whitelist of input characters.
- Avoid using Old versions of software
What Are Owasp Webgoat And Webscarab
WebGoat: It serves as a benchmark for testing security technologies against known problems and is a learning tool for application security. It is a J2EE web-based application built on the basis of tomcat and JDK 1.5 that is divided into “Security Lessons”
WebScarab: A framework for evaluating HTTP/HTTPS traffic is called WebScarab. It performs a number of tasks, including fragment analysis, observing browser and server traffic, session ID analysis, manual intercept, and locating new URLs on each page browsed.
Don’t Miss: How To Prepare For Product Manager Interview
Why Do You Want To Work For This Company
This question allows you to demonstrate your knowledge of the company you’re applying for and the reasons you think the company might be compatible to you. Before going to the interview, make sure to research the company and come prepared with a list of reasons to work there that might excite you.
Example:”I’ve been following this company’s work and progress for a little while now, and I love what you’re achieving in the world of application security. From your work and coding on password protection software to your work with individual clients, you’ve shown yourselves to be an essential part of the app security world. I would love to be a part of this team and your company’s continued development.”
What Is A Computer Virus
A virus is a malicious software that is executed without the userâs consent. Viruses can consume computer resources, such as CPU time and memory. Sometimes, the virus makes changes in other computer programs and insert its own code to harm the computer system.
A computer virus may be used to:
- Access private data like user id and passwords
- Display annoying messages to the user
- Corrupt data in your computer
- Log the userâs keystrokes
Read Also: Occupational Therapy Interview Questions For Clients
Why Learn A Cyber Security Course
Web Application Security Interview Questions And Answers
Prepare for the types of questions you are likely to be asked when interviewing for a position where Web Application Security will be used.
As the number of web applications continues to grow, so does the need for qualified individuals who can ensure the security of these applications. When applying for a position in web application security, you can expect the interviewer to ask questions about your experience and knowledge in this area. In this article, we review some of the most common questions asked during a web application security interview and provide tips on how to answer them.
Recommended Reading: What Should You Take To An Interview
Have You Ever Countered Sensitive Data Exposure How Can It Be Mitigated
There are several means of mitigating the risk of sensitive data exposure, which is a big concern in web security. The most straightforward and obvious one is encrypting data to protect it from cyber-attacks. Sensitive data shouldnt be stored poorly or unnecessarily but instead discarded as fast as possible. Other ways include preparing a threat model for data security during transit and at test, storing passwords with an algorithm for password protection, and disabling auto-completion of forms that collect sensitive data.
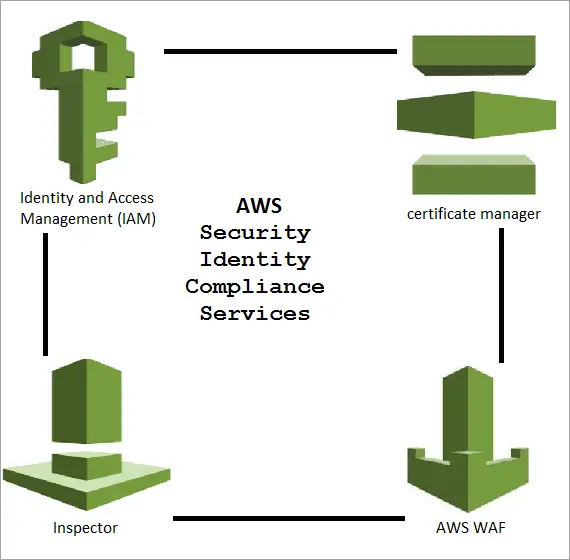
What Do You Mean By Cybersecurity
Cybersecurity is the protection of critical systems and sensitive information from digital security threats. The field of cybersecurity encompasses infrastructure security, network security, cloud security, and application security. Cybersecurity protocols are responsible for preventing security breaches that could compromise an organizations data and infrastructure. Cybersecurity encompasses security engineering and architecture, incident response, consulting, testing, and ethical hacking.
Recommended Reading: Where Can I Watch The Interview
Q: What Is Security Testing
Answer:
Security testing can be considered most important in all type of software testing. Its main objective is to find vulnerabilities in any software based application and protect their data from possible attacks or intruders.
As many applications contains confidential data and needs to be protected being leaked. Software testing needs to be done periodically on such applications to identify threats and to take immediate action on them.
Basic Website And It Questions
Start the interview by making sure the candidate understands how websites and applications work in general. Here, youre probing to see whether they understand protocols, networking layers, browsers, servers, databases, data at rest, data in transit, and the like. Here are a few classic interview questions to assess their understanding of these topics:
Question: Explain what happens when you enter google.com in a browsers address bar. This is a very open-ended question. The right answer varies per the job requirements. But in general, the candidate should have a fair understanding of DNS, DHCP, ARP, TCP and SSL/TLS handshakes, proxy, cookies, session management, HTTP methods, GET/POST, and so on.
Question: Are you a Mac/Windows/Linux person? Which OS is most secure? Trick question! No OS is completely secure. A lot depends on how its patched, configured, and managed. You can ask follow-up questions on OS hardening, patching, configuration management, and so on.
| Tip: Start with open-ended questions and then drill down into specifics based on the candidates responses and the job requirements. Trivia questions like What is the port number for SMTP? are not helpful. |
You May Like: How To Record A Phone Interview
What Do You Like Best About Your Current Role
When the interviewer asks this question, it gives you an opportunity to talk about why you love working as an application security programmer and show the interviewer your positive attitude toward the job. It can also be helpful to mention specific examples of how well you collaborate with your current team.
Example:”My programming team has been the best part of my current role. Every day they come to work with a positive attitude. This helps us collaborate better together and creates an atmosphere that welcomes questions and support. I am excited to join a similar team here at Web Security.”
Why Are You Leaving Your Current Role
It’s important to approach this question with a positive tone. When you answer this question, focus on your search for new opportunities and finding a company that allows you to continue to improve your skills and knowledge. This can help you demonstrate your respect for your current employer while showing your excitement for a new position.
Example:”Though my time at Foltess Security has been wonderful, I am looking for new opportunities to continue to learn and grow in application security. I believe that this company can give me that opportunity and strengthen my skills as a computer programmer.”
Also Check: Where To Shop For Interview Clothes